How connect to the Tor network via bridge on Linux
June 7, 2021
Some ISPs are blocking Tor. They can use various approaches, for example, block connections to all IPs of the Tor network, or by analyzing traffic and, if it is identified as belonging to the Tor network, block it.
Repeaters can be used to bypass this blockage. The bridge is one of the types of repeaters. Since not all bridge IP addresses are known, there is a chance to bypass Tor's blocking.
You need to get a list of current IP addresses. To do this, follow the link: https://bridges.torproject.org/options
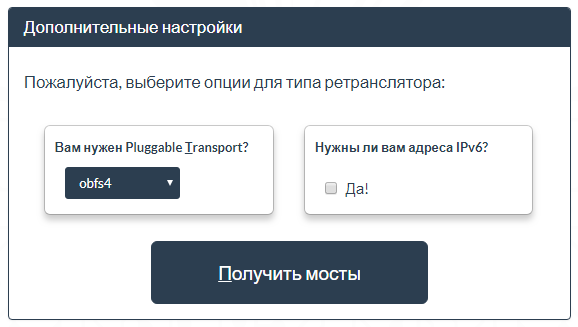
Select obfs4 and click the Get Bridges Button:
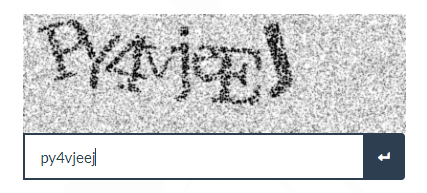
Enter captcha:
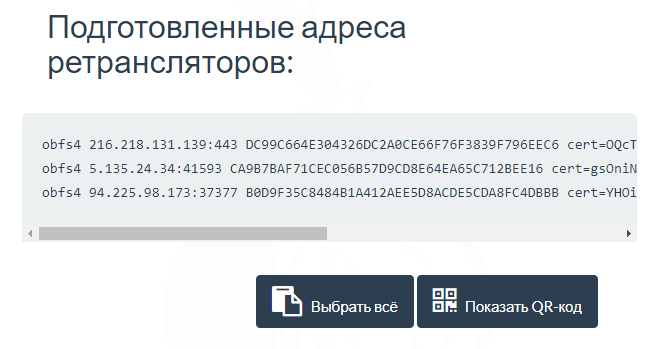
You will be given a list of three addresses. Copy one of these lines.
Another way to get bridges is to send an email to bridges@torproject.org. Please note that you must submit an email request using one of the listed services: Riseup, Gmail, or Yahoo.
An example of my lines:
obfs4 185.220.101.103:52103 092D75D78FCBCD4487512FF09D077302B9EA5965 cert=p9L6+25s8bnfkye1ZxFeAE4mAGY7DH4Gaj7dxngIIzP9BtqrHHwZXdjMK0RVIQ34C7aqZw iat-mode=2 obfs4 45.33.1.189:9123 F9DFF618E7BA6C018245D417F39E970C2F019BAA cert=mDZuXuqSTjX1OjN7zLybTYzNi0A21A7G0DRNmW79029cSvLYSOk/KhGftcnmxruTmhRfZQ iat-mode=0 obfs4 199.26.245.64:34623 A30297A915AF69F84A2806E30E34E5856E74970C cert=qZ/wyRxyOjnpvKsoKY6bcpAIFTGhLPLUZiqTJsSlipBAzkDesnmWXOp+rVSXlZcYVu7EBw iat-mode=0
Install the required packages.
In Debian derivatives (Kali Linux, Linux Mint, Ubuntu), this is done with the command:
sudo apt install tor obfs4proxy
On Arch Linux derivatives (BlackArch, Manjaro), this is done with the command:
sudo pacman -S tor obfs4proxy
To the file /etc/tor/torrc
sudo gedit /etc/tor/torrc
Add the following lines:
ClientTransportPlugin obfs4 exec /usr/bin/obfs4proxy Bridge obfs4 185.220.101.103:52103 092D75D78FCBCD4487512FF09D077302B9EA5965 cert=p9L6+25s8bnfkye1ZxFeAE4mAGY7DH4Gaj7dxngIIzP9BtqrHHwZXdjMK0RVIQ34C7aqZw iat-mode=2 UseBridges 1
In the line that starts with Bridge, enter your bridge details.
Start the tor service:
sudo systemctl restart tor
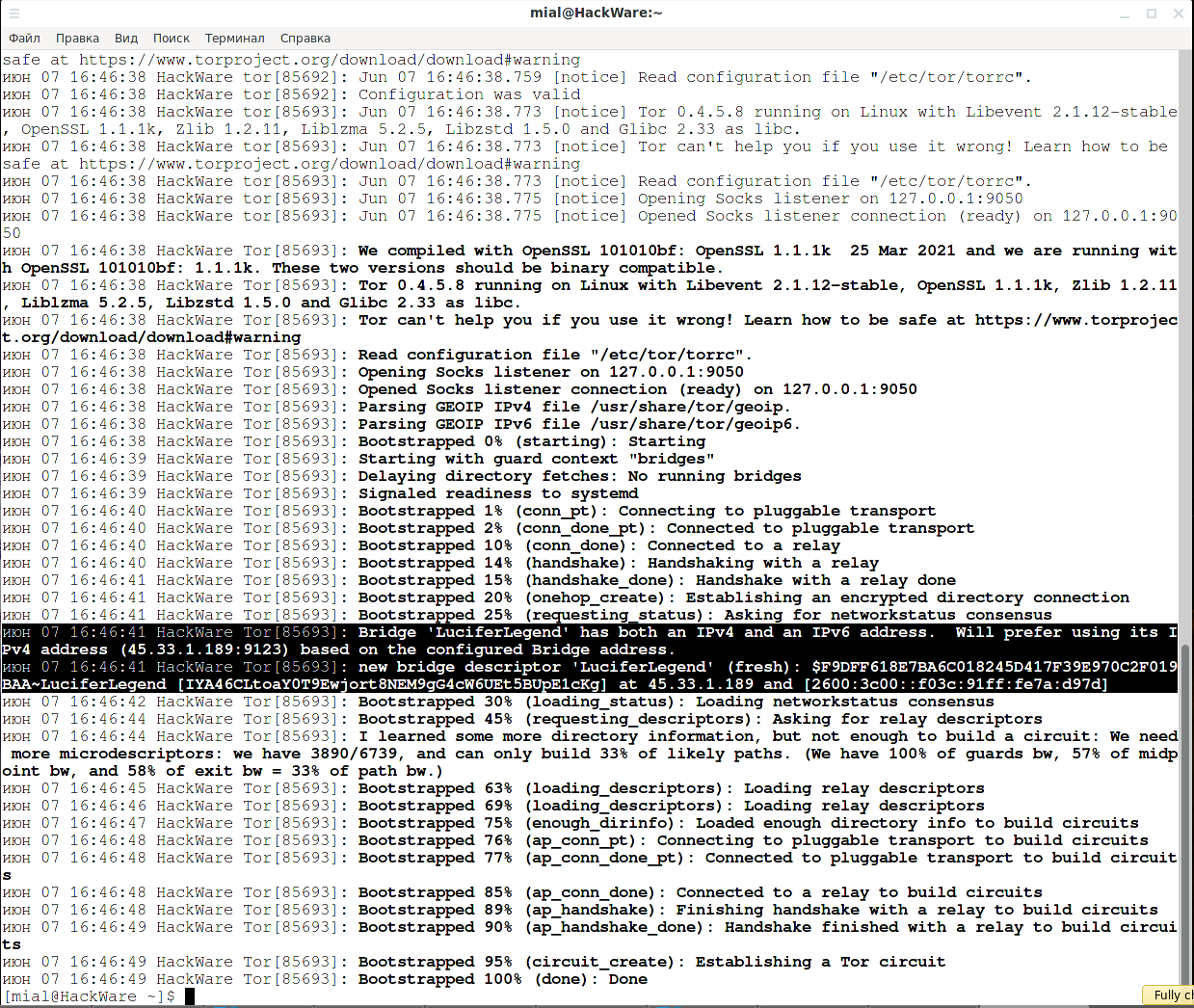
If the service started without errors, look at the Tor log:
sudo journalctl -b --no-pager /usr/bin/tor
Notice the lines that mention the bridge:
Bridge 'LuciferLegend' has both an IPv4 and an IPv6 address. Will prefer using its IPv4 address (45.33.1.189:9123) based on the configured Bridge address. new bridge descriptor 'LuciferLegend' (fresh): $F9DFF618E7BA6C018245D417F39E970C2F019BAA~LuciferLegend [IYA46CLtoaY0T9Ewjort8NEM9gG4cW6UEt5BUpE1cKg] at 45.33.1.189 and [2600:3c00::f03c:91ff:fe7a:d97d]
If you do not have root rights and cannot edit the /etc/tor/torrc file, then this is not an obstacle to connecting to the Tor network via a bridge.
Create a settings file anywhere you have write permissions:
gedit settings.txt
And copy the following lines into it (replace the bridge parameters with yours):
ClientTransportPlugin obfs4 exec /usr/bin/obfs4proxy Bridge obfs4 77.116.217.120:59126 5A1C6F3FEB89849001EDBFF45C17025E9C6324A3 cert=NyiABUP2ym213/zjXUVcBqe/HaGHnz6no30XXynqkDCFo9+bKTt+8JdWN6zUygHESaVPEw iat-mode=0 UseBridges 1
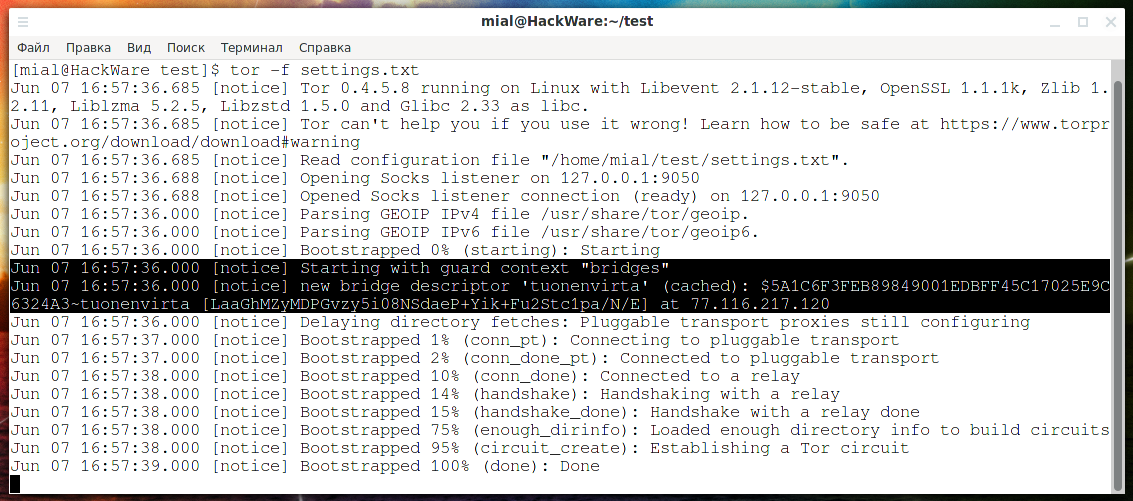
Run like this:
tor -f settings.txt
As you can see from the following lines, the connection to the Tor network is made using a bridge:
Jun 07 16:57:36.000 [notice] Starting with guard context "bridges" Jun 07 16:57:36.000 [notice] new bridge descriptor 'tuonenvirta' (cached): $5A1C6F3FEB89849001EDBFF45C17025E9C6324A3~tuonenvirta [LaaGhMZyMDPGvzy5i08NSdaeP+Yik+Fu2Stc1pa/N/E] at 77.116.217.120
Related articles:
- How to connect to Tor with OpenVPN (61.1%)
- How to download YouTube videos on Windows and Linux (GUI without third party services) (55.9%)
- How to install the latest version of Tor on Ubuntu (55.9%)
- How to change configuration files when migrating from OpenVPN 2.4.* to OpenVPN 2.5.* (55.3%)
- How to use OpenVPN with TCP protocol (55.3%)
- How to save MySQL query results in a new table (RANDOM - 50%)